Wireshark - Ethernet and ARP
Introduction
In this lab, we’ll investigate the Ethernet protocol and the ARP protocol. Before beginning this lab, you’ll probably want to review sections 6.4.1 (Link-layer addressing and ARP) and 6.4.2 (Ethernet) in the text.
RFC 826 contains the gory details of the ARP protocol, which is used by an IP device to determine the IP address of a remote interface whose Ethernet address is known.
Capturing and analyzing Ethernet frames
Let’s begin by capturing a set of Ethernet frames to study. Do the following:
-
First, make sure your browser’s cache is empty. The easiest way is to use "Incognito mode".
-
Start up the Wireshark packet sniffer
-
Enter the following URL into your browser
http://wireshark.grydeske.net/file3.htmlYour browser should display the rather lengthy US Bill of Rights. -
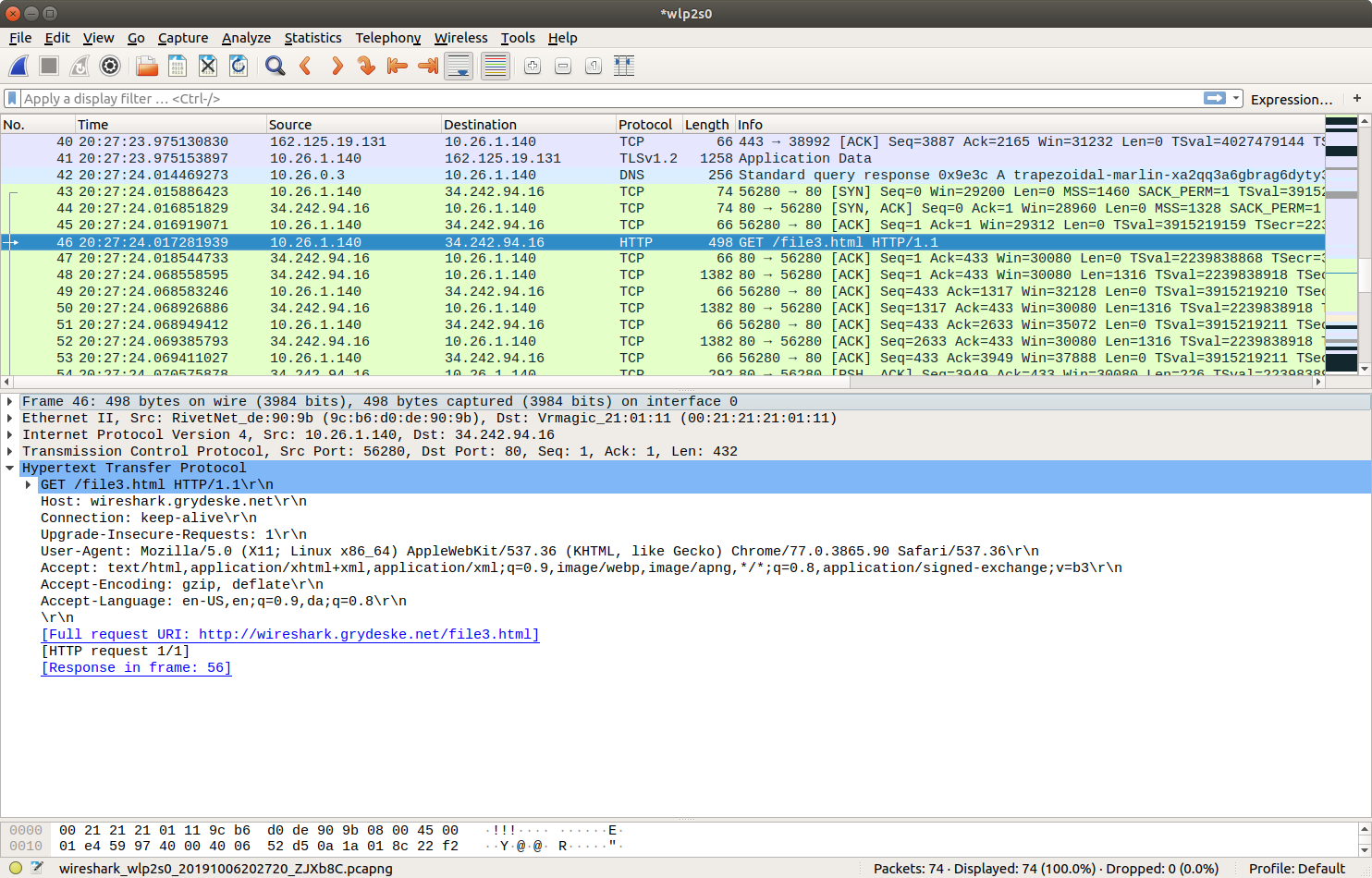
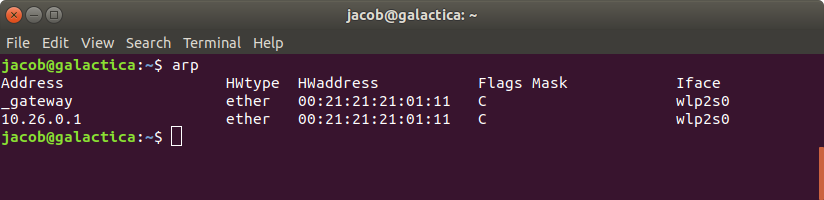
Stop Wireshark packet capture. First, find the packet numbers (the leftmost column in the upper Wireshark window) of the HTTP GET message that was sent from your computer to wireshark.grydeske.net, as well as the beginning of the HTTP response message sent to your computer by wireshark.grydeske.net. You should see a screen that looks something like this (where packet 4 in the screen shot below contains the HTTP GET message)
Since this lab is about Ethernet and ARP, we’re not interested in IP or higher- layer protocols. So let’s change Wireshark’s “listing of captured packets” window so that it shows information only about protocols below IP. To have Wireshark do this, select Analyze→Enabled Protocols. Then uncheck the IP box (IPv4 + IPv6) and select OK. You should now see an Wireshark window that looks like:

In order to answer the following questions, you’ll need to look into the packet details and packet contents windows (the middle and lower display windows in Wireshark).
Select the Ethernet frame containing the HTTP GET message. (Recall that the HTTP GET message is carried inside of a TCP segment, which is carried inside of an IP datagram, which is carried inside of an Ethernet frame; reread section 1.5.2 in the text if you find this encapsulation a bit confusing). Expand the Ethernet II information in the packet details window. Note that the contents of the Ethernet frame (header as well as payload) are displayed in the packet contents window.
Answer the following questions, based on the contents of the Ethernet frame containing the HTTP GET message.
-
What is the 48-bit Ethernet address of your computer?
-
What is the 48-bit destination address in the Ethernet frame? Is this the Ethernet address of wireshark.grydeske.net? (Hint: the answer is no). What device has this as its Ethernet address? [Note: this is an important question, and one that students sometimes get wrong. Re-read pages 468-469 in the text and make sure you understand the answer here.]
-
Give the hexadecimal value for the two-byte Frame type field. What upper layer protocol does this correspond to?
-
How many bytes from the very start of the Ethernet frame does the ASCII “G” in “GET” appear in the Ethernet frame?
Next, answer the following questions, based on the contents of the Ethernet frame containing the first byte of the HTTP response message.
-
What is the value of the Ethernet source address? Is this the address of your computer, or of wireshark.grydeske.net (Hint: the answer is no). What device has this as its Ethernet address?
-
What is the destination address in the Ethernet frame? Is this the Ethernet address of your computer?
-
Give the hexadecimal value for the two-byte Frame type field. What upper layer protocol does this correspond to?
-
How many bytes from the very start of the Ethernet frame does the ASCII “O” in “OK” (i.e., the HTTP response code) appear in the Ethernet frame?
The Address Resolution Protocol
In this section, we’ll observe the ARP protocol in action. We strongly recommend that you re-read section 6.4.1 in the text before proceeding.
ARP Caching
Recall that the ARP protocol typically maintains a cache of IP-to-Ethernet address translation pairs on your computer The arp command (in both MSDOS and Linux/Unix) is used to view and manipulate the contents of this cache. Since the arp command and the ARP protocol have the same name, it’s understandably easy to confuse them. But keep in mind that they are different - the arp command is used to view and manipulate the ARP cache contents, while the ARP protocol defines the format and meaning of the messages sent and received, and defines the actions taken on message transmission and receipt.
Let’s take a look at the contents of the ARP cache on your computer:
-
Windows: The arp command is in c:\windows\system32, so type either
arporc:\windows\system32\arpin the command line (without quotation marks). -
Linux/Unix/MacOS: The executable for the arp command can be in various places. Popular locations are /sbin/arp (for linux) and /usr/etc/arp (for some Unix variants). You can use just
arp
The Windows arp command with no arguments will display the contents of the ARP cache on your computer. Run the arp command.
-
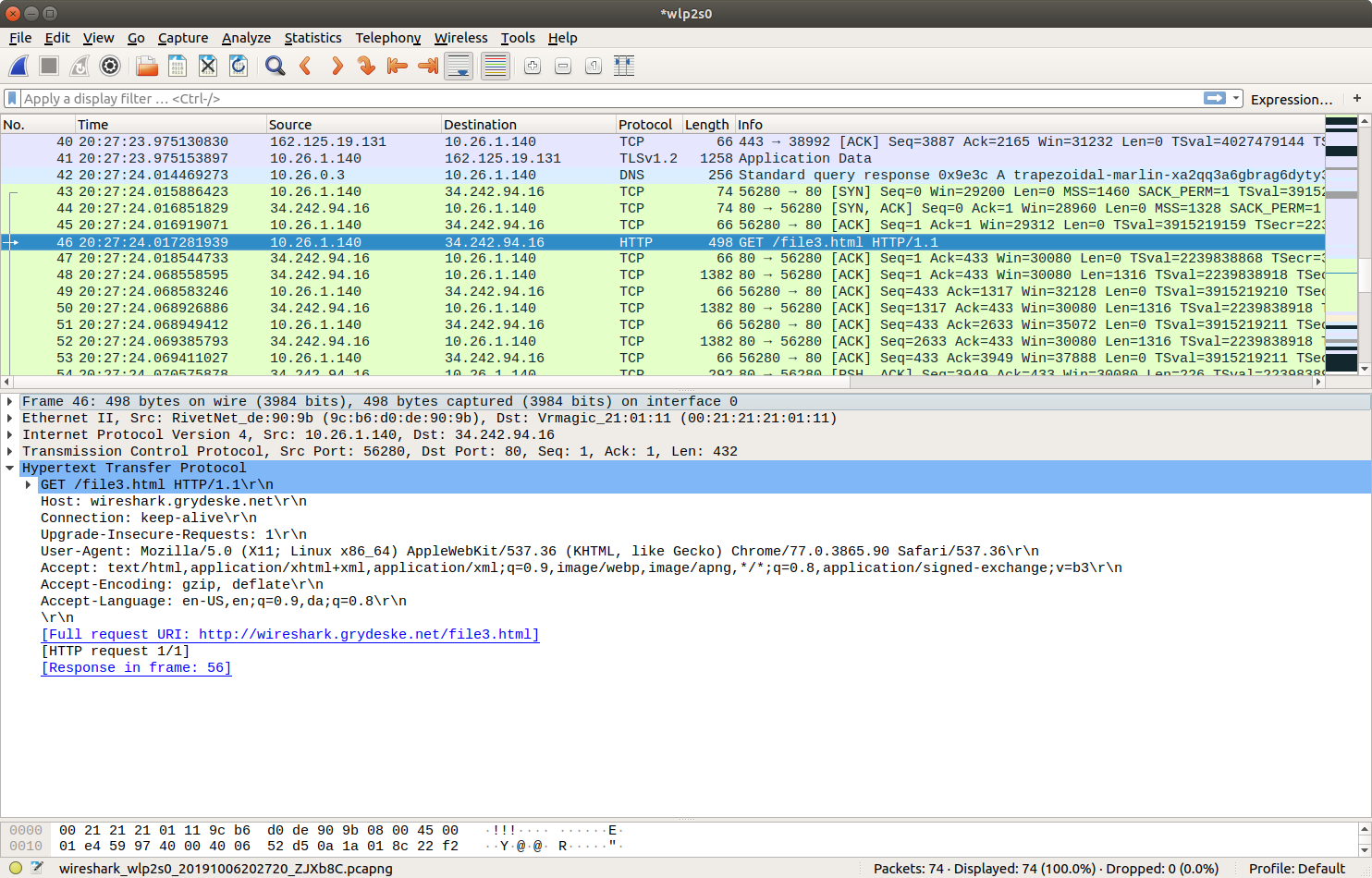
Write down the contents of your computer’s ARP cache. What is the meaning of each column value?
In order to observe your computer sending and receiving ARP messages, we’ll need to clear the ARP cache, since otherwise your computer is likely to find a needed IP-Ethernet address translation pair in its cache and consequently not need to send out an ARP message.
-
Windows: The
arp –d *command will clear your ARP cache. The –d flag indicates a deletion operation, and the * is the wildcard that says to delete all table entries. -
Linux/Unix/MacOS:Thesudo arp –d <IP address>will clear an entry from your ARP cache. In order to run this command you’ll need root privileges.
Observing ARP in action
Do the following:
-
Clear your ARP cache, as described above.
-
Next, make sure your browser’s cache is empty. Use a new incognito window
-
Start up the Wireshark packet sniffer Enter the following URL into your browser
http://wireshark.grydeske.net/file3.htmlYour browser should again display the rather lengthy US Bill of Rights. -
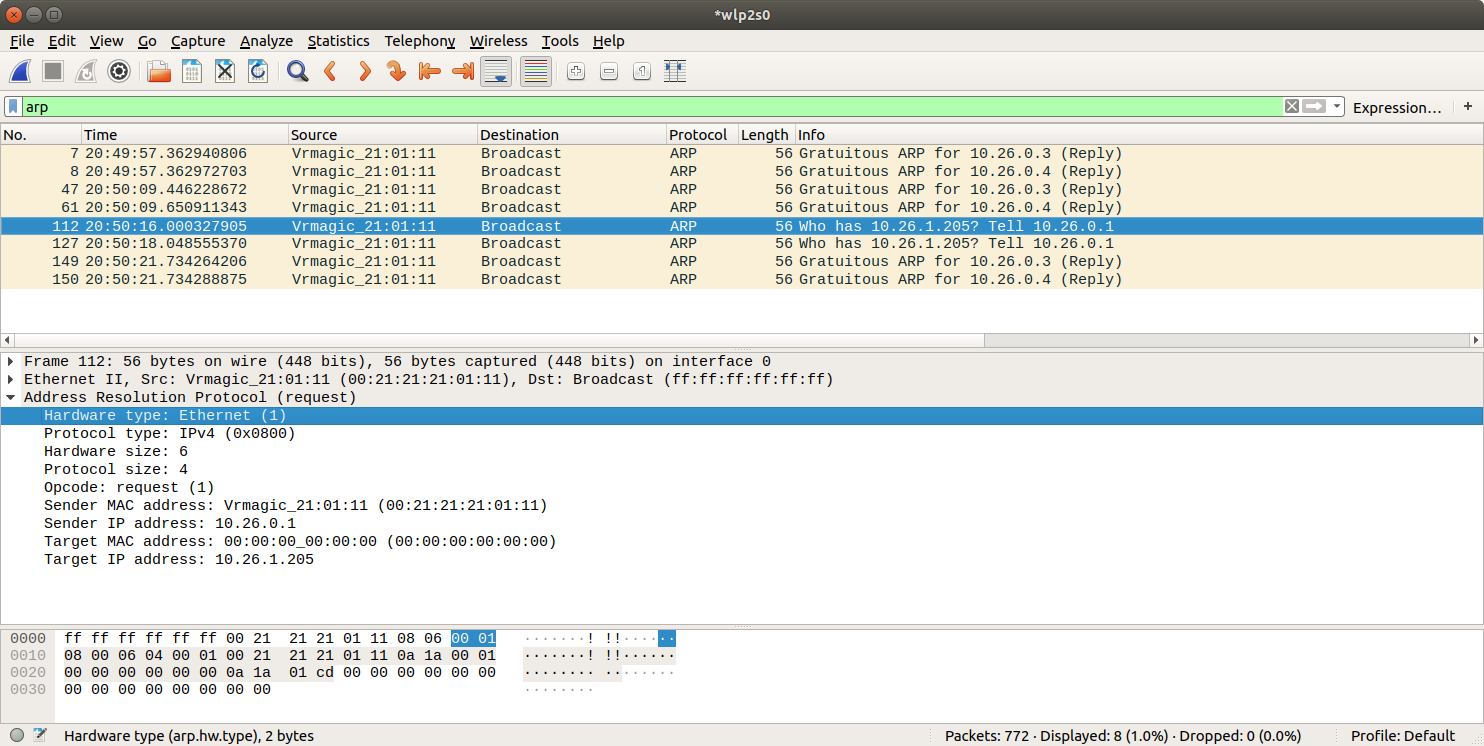
Stop Wireshark packet capture. Again, we’re not interested in IP or higher-layer protocols, so change Wireshark’s “listing of captured packets” window so that it shows information only about protocols below IP. To have Wireshark do this, select Analyze→Enabled Protocols. Then uncheck the IP box and select OK. You should now see an Wireshark window that looks like:
-
What are the hexadecimal values for the source and destination addresses in the Ethernet frame containing the ARP request message?
-
Give the hexadecimal value for the two-byte Ethernet Frame type field. What upper layer protocol does this correspond to?
-
Download the ARP specification from https://tools.ietf.org/html/rfc826. A readable, detailed discussion of ARP is also at http://www.erg.abdn.ac.uk/users/gorry/course/inet-pages/arp.html.
-
How many bytes from the very beginning of the Ethernet frame does the ARP opcode field begin?
-
What is the value of the opcode field within the ARP-payload part of the Ethernet frame in which an ARP request is made?
-
Does the ARP message contain the IP address of the sender?
-
Where in the ARP request does the “question” appear – the Ethernet address of the machine whose corresponding IP address is being queried?
-
-
Now find the ARP reply that was sent in response to the ARP request.
-
How many bytes from the very beginning of the Ethernet frame does the ARP opcode field begin?
-
What is the value of the opcode field within the ARP-payload part of the Ethernet frame in which an ARP response is made?
-
Where in the ARP message does the “answer” to the earlier ARP request appear – the IP address of the machine having the Ethernet address whose corresponding IP address is being queried?
-
-
What are the hexadecimal values for the source and destination addresses in the Ethernet frame containing the ARP reply message?
